CYBERSECURITY FOR SMBs:
ENTERPRISE-GRADE SECURITY OPERATIONS AT SMB SCALE
SMBs face the same threats as the Fortune 500, and the same security operations are required to stop them. RADICL is your enterprise security operations team. 24/7 monitoring, prioritized remediations and full incident response.
Why SMBs Get Targeted
For founders, cybersecurity becomes urgent when it turns into downtime, lost revenue, and missed commitments—not when an alert fires.

You’re an easier path to money
Attackers assume SMBs have weaker defenses and slower response.

You’re an easier path to bigger targets
SMBs often sit in supply chains (e.g. primes and regulated customers), so compromising you can open doors.

Requirements are rising—even if your team isn’t
Cyber insurance, customer security reviews, and compliance expectations are increasing, and they increasingly require proof.
Vendors have provided SMBs with “Best effort,” IT support and tools based approaches. They will not stop motivated threat actors, nation state threats or small incidents escalating into major business outages. RADICL closes the gap with best in class point tools, a proprietary platform and enterprise-grade security operations purpose built for SMBs.
How CSaaS Helps You Get Secure
Most SMBs start with a mix of internal IT, a few tools, and sometimes an MSP. The gap shows up when you need 24/7 coverage and proof—without hiring a full security team.
Cybersecurity-as-a-Service (CSaaS) is a managed operating model that delivers hardening + detection + response + compliance-ready reporting through an owned platform and career security experts.
People (Coverage)
24/7 eyes on threats
Expertise to investigate and lead response
Not just alerts—answers
Process (Execution)
Prioritized remediation and follow-through
Incident playbooks and tasking
Coordination with your IT team/MSP
Proof (Confidence)
Visibility into what’s happening
Reporting leaders/insurers can use
Evidence for compliance when required
RADICL delivers CSaaS powered by an owned platform and career security experts. Built for SMB reality—enterprise-grade outcomes without enterprise headcount.
Where most SMBs get stuck (and how RADICL closes the gap)
If security feels like an endless backlog, the issue usually isn’t effort—it’s lack of prioritization, ownership, and follow-through.

How RADICL works
Signals In
We ingest the telemetry needed to detect threats across endpoint, identity, and network activity (based on scope).
Triage
Our vSOC filters noise and confirms what’s real.
Investigate
We determine impact and next steps and document findings clearly.
Respond + Assign Tasks
We lead response and assign precise remediation actions (to your IT team or MSP as needed).
Track to Closure
We confirm progress and document outcomes so issues don’t linger.
Improve Resiliency
We harden what matters most—so the same issue doesn’t repeat.
Already have an MSP? Here’s how we work together
RADICL is designed to complement MSP-led IT—not disrupt it.

RADICL owns security operations outcomes
Triage, investigation, response leadership, and follow-through.
Your MSP keeps IT execution moving
Configuration changes, patching, and day-to-day IT delivery.

No confusion on who does what
We define a shared responsibility model for your environment so execution is fast and cooperative.
Get the Visibility You Deserve
At RADICL, operational transparency is a core value. We want you to know exactly what we are doing to keep you secure and compliant. As a customer, you should demand no less from a managed security services provider. Through transparency comes accountability and trust.
Our Protection Delivered Dashboard
Watch this video to learn how with RADICL, you'll enjoy real-time visibility into how we are:
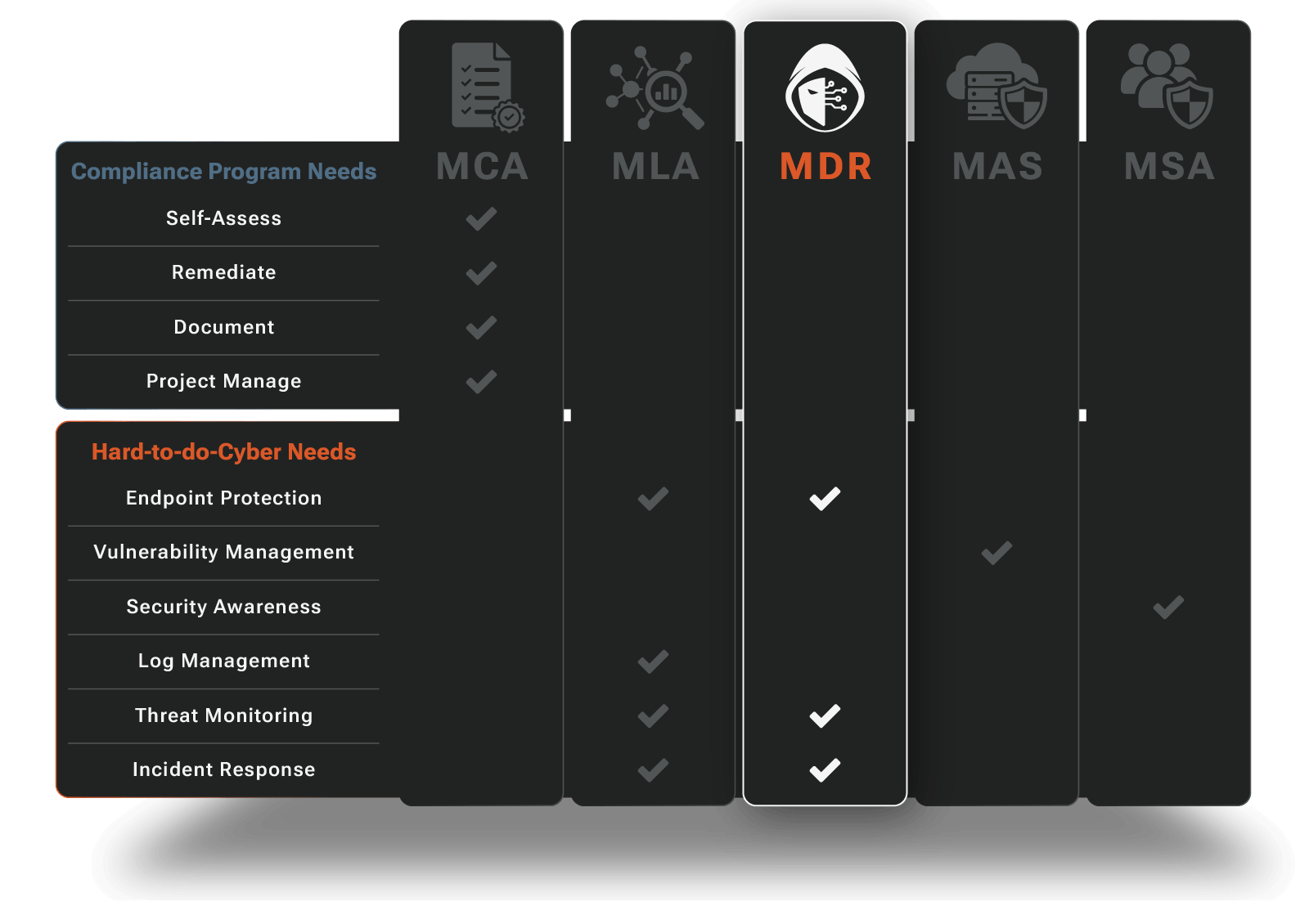
Our Solutions
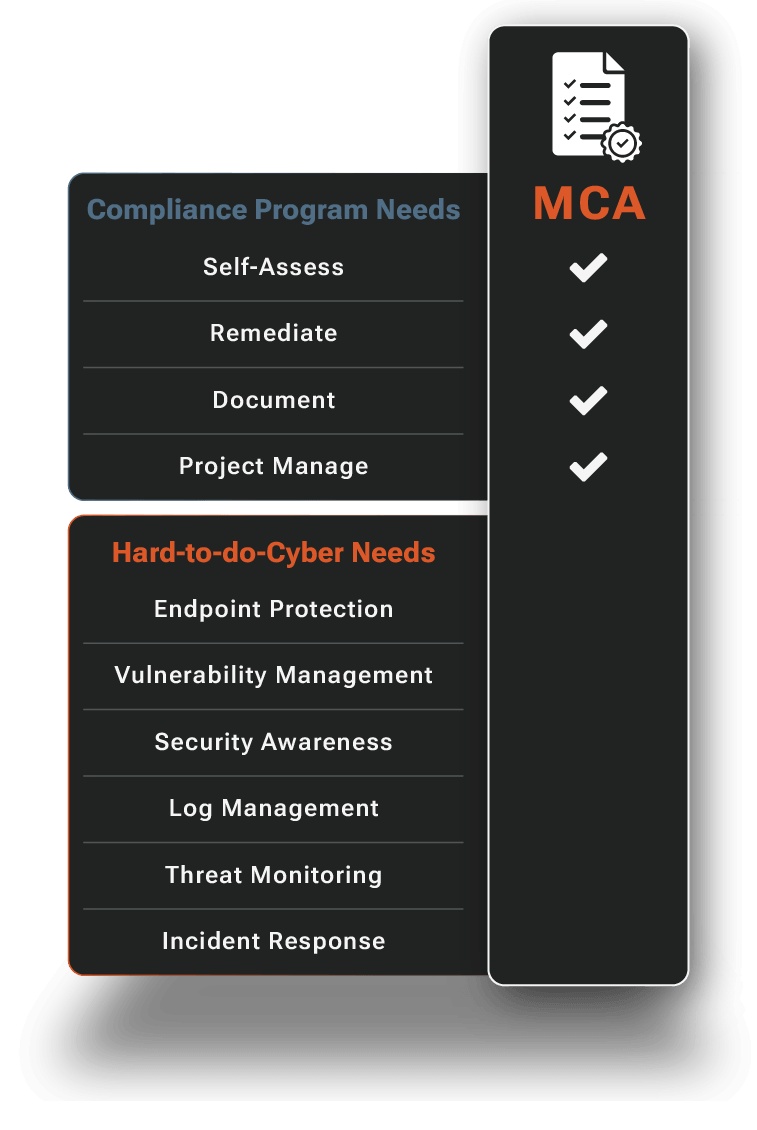
Managed Compliance Adherence for CMMC and NIST
CMMC and NIST 800‑171 (and similar frameworks) are now a cost of doing business. We keep the cost low. Our Managed Compliance Adherence expertly guides and manages your compliance journey. Our compliance experts combined with agentic automation fast track readiness and reduce audit anxiety.
- Self-Assessments Guided and Made Easy
- CMMC and NIST Adherence Gaps Quickly Closed
- Audit Trail and Evidence Capture
- Compliance Posture Clarity
- External Audit Preparedness & Efficiency
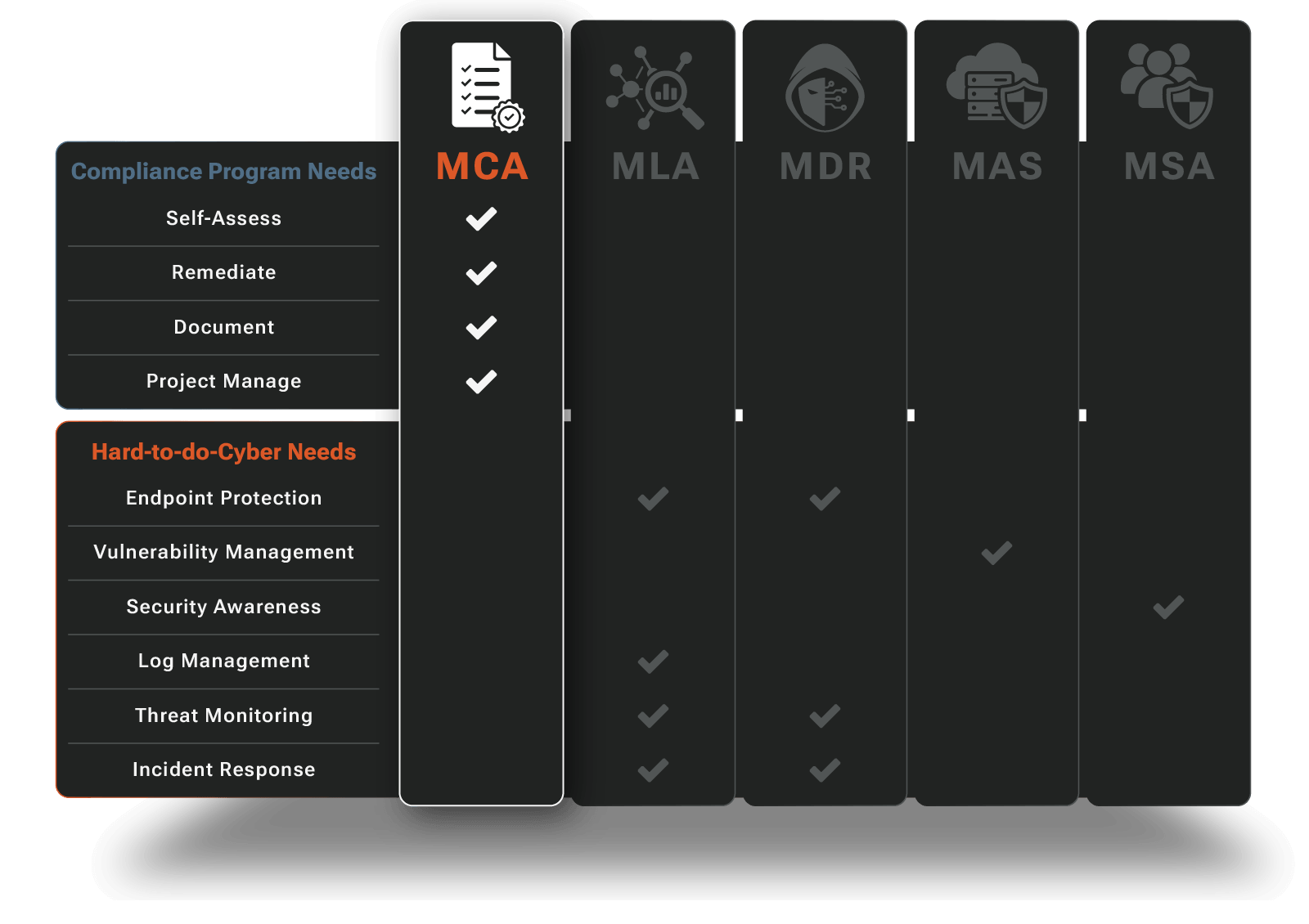
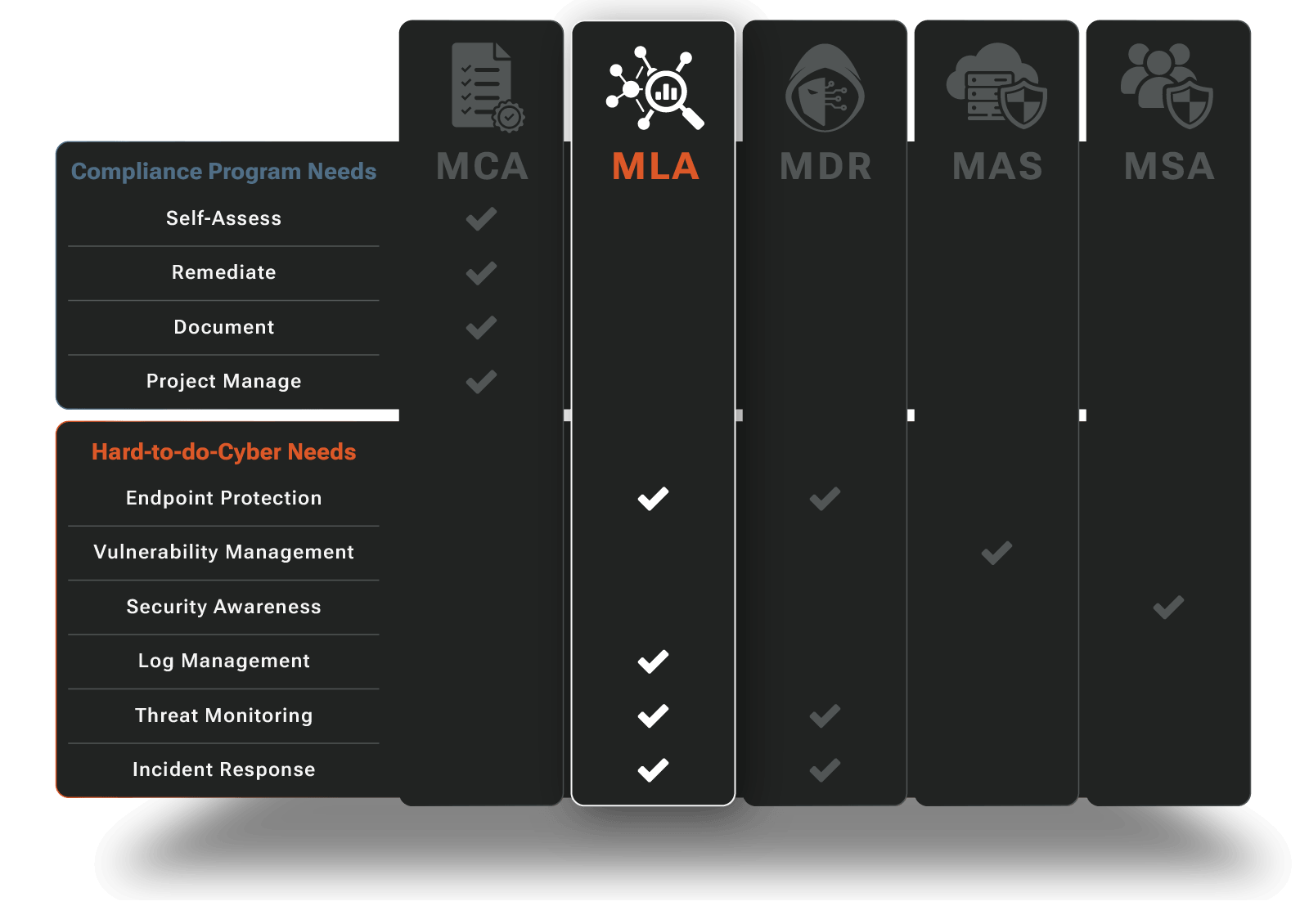
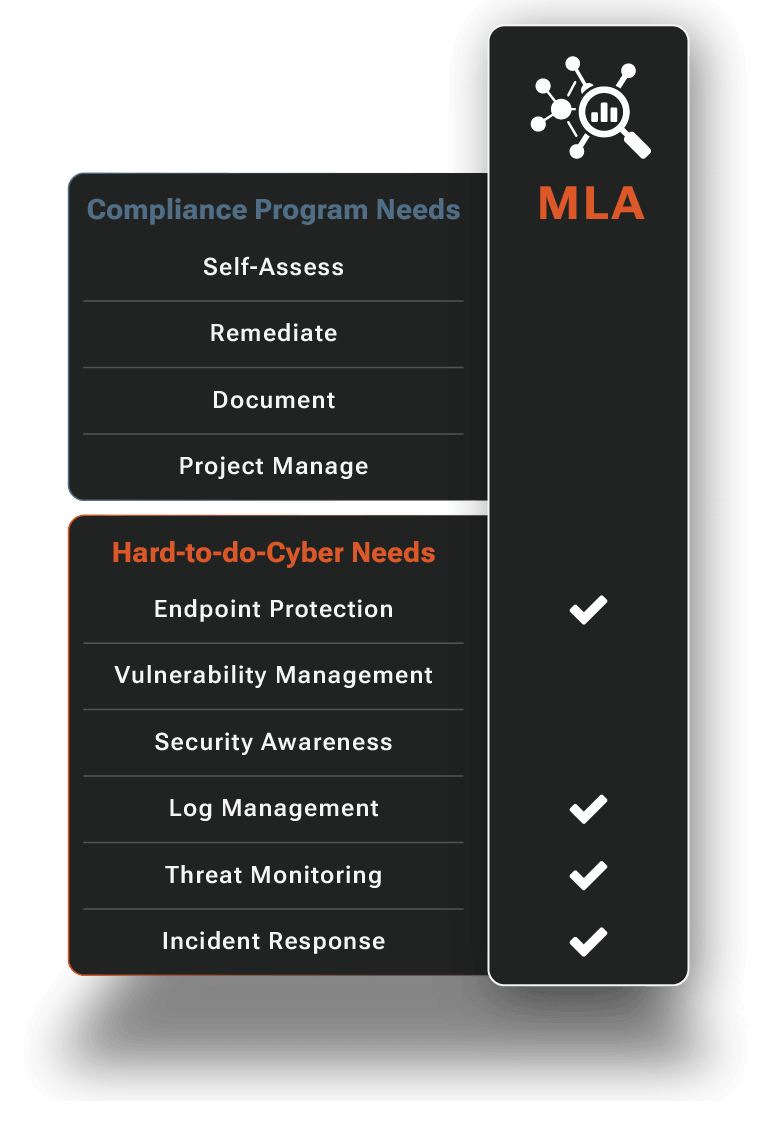
Managed Log Analytics
Investigations and audits require comprehensive visibility, but aggregating logs across your entire environment can be complex and expensive. Not with us.
We handle the entire log management lifecycle, from collection and normalization to long-term retention and searchable investigation capabilities. Our platform gives you the log foundation needed for effective detection & response while meeting strict compliance requirements.
- 14 or 90-Day Velocity Search + 1-Year Archive
- AI-Assisted Natural Language Search
- Hunt UX with vSOC Incident Escalation
- On-Demand Compliance Evidence Export
- vSOC-Managed Ingestion & Health Monitoring
Managed Detection
and Response
Advanced endpoint protection, military-grade threat hunting, and 24/7 incident response ensure your company is safe from ransomware, data theft, financial fraud, and other high-impact cyber risks while supporting CMMC and NIST 800‑171 compliance.
- Endpoints and Servers Protected
- Evasive & Embedded Threats Detected and Stopped
- 24/7 Security Operations Has Your Back
- Incidents Managed End-to-End
- Virtual CISO By Your Side
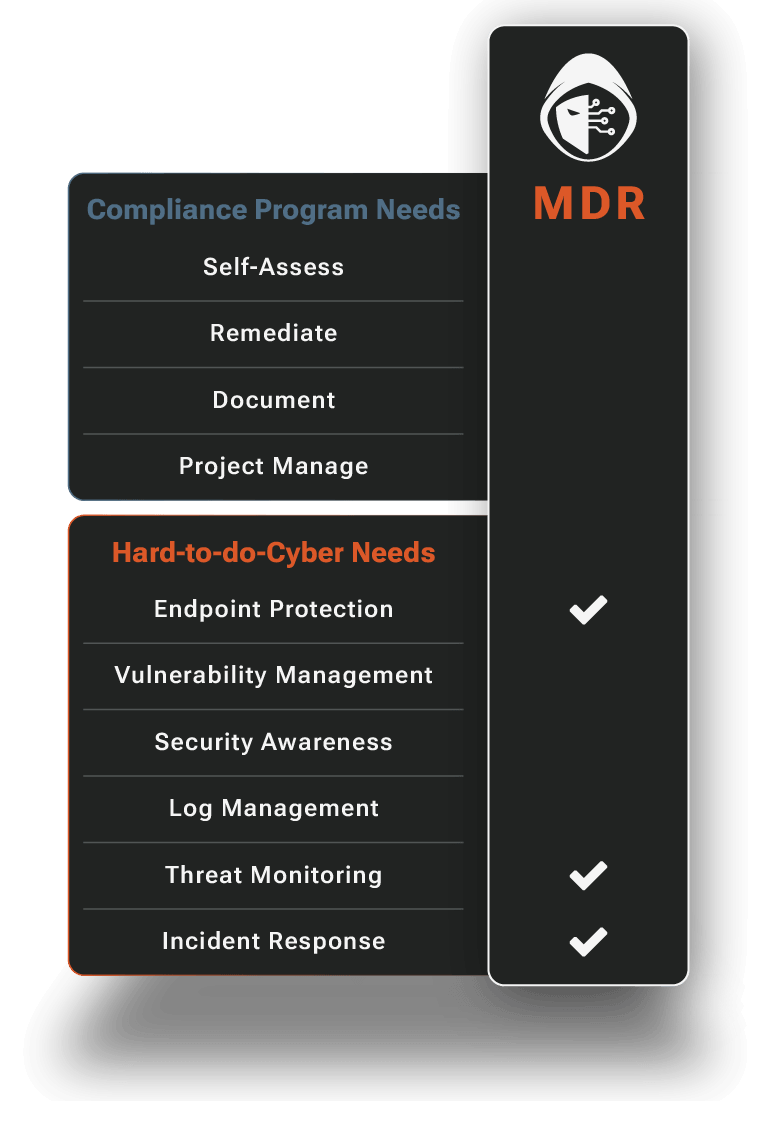
MDR: Endpoint
MDR: Endpoint is the foundation of our MDR offering. We deploy, optimize, and maintain leading EDR technologies (for example, CrowdStrike, SentinelOne, and Microsoft Defender) across your laptops, workstations, and server infrastructure. We deploy custom detection analytics to spot threats out-of-the box EDR miss.
MDR: Identity
With MDR: Identity, we ingest and analyze data from Identity and user activity data sources like Microsoft 365 and Google Workspace. We monitor authentication activity, access to sensitive data and files, and email behavior to detect account takeover, inbox compromise, and data exfiltration.
MDR: Network
MDR: Network collects alarms and threat data from physical, wireless and cloud network infrastructure. We correlate this with endpoint and identity telemetry to fully investigate suspicious behavior and provide defense‑in‑depth coverage.
How RADICL Detects and Responds
Below is a closer look at our Managed Detection and Response (MDR) operations. This is how we turn signals into 24/7 investigations, containment, and tracked remediation.
Managed Attack Surface
Threat actors leverage vulnerabilities to get a foot in the door and expand their presence. Our Managed Attack Surface offering persistently reduces your exposure so your organization becomes a much harder target for both opportunistic and targeted attacks.
- Endpoint and Server Vulnerabilities Detected and Prioritized
- Pragmatic and Manageable Remediation Pace
- Accelerated Critical Fix Response
- Expert Guidance and Collaboration With Your IT/MSP Partners
- Closed Loop “Fixed” Visibility
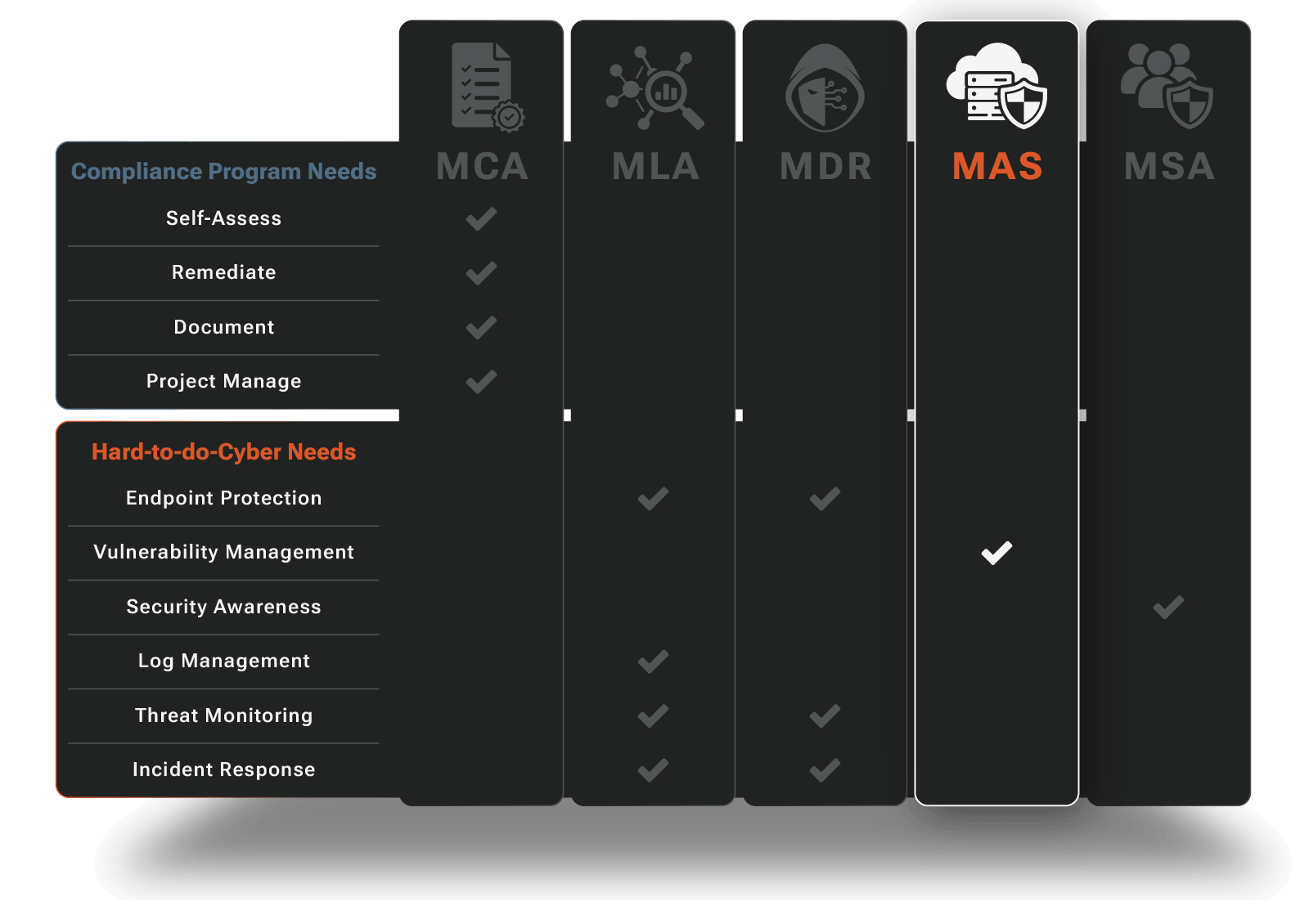
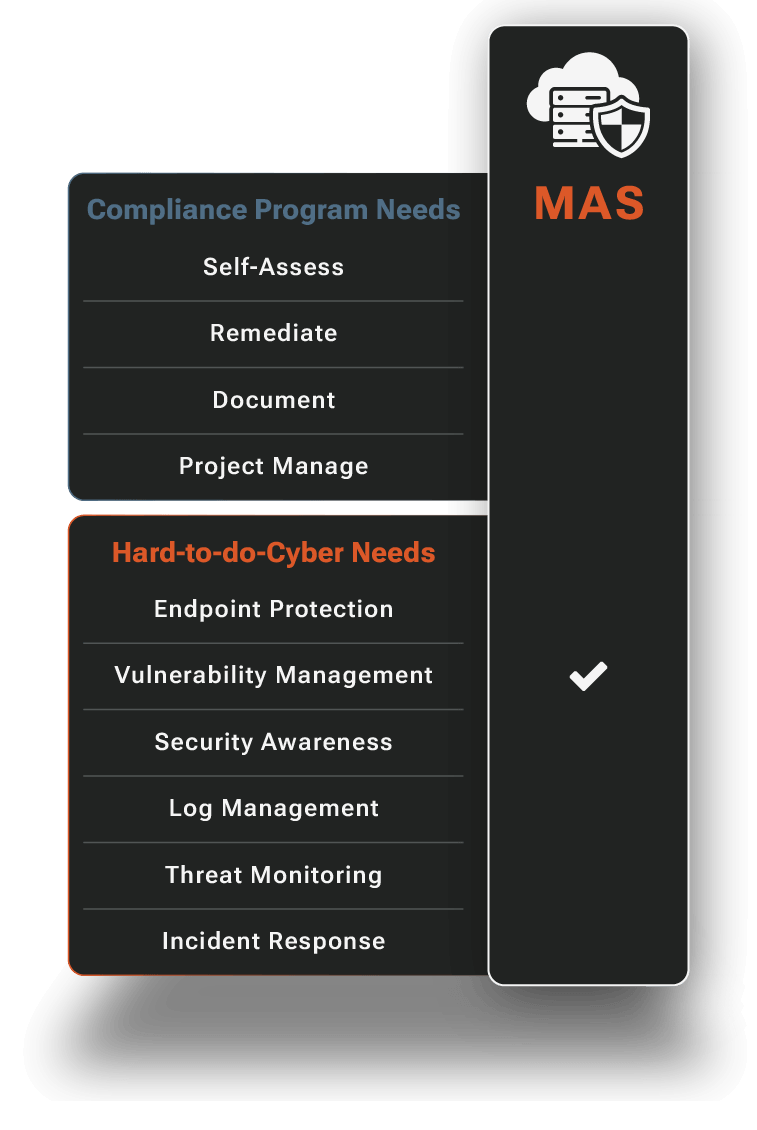
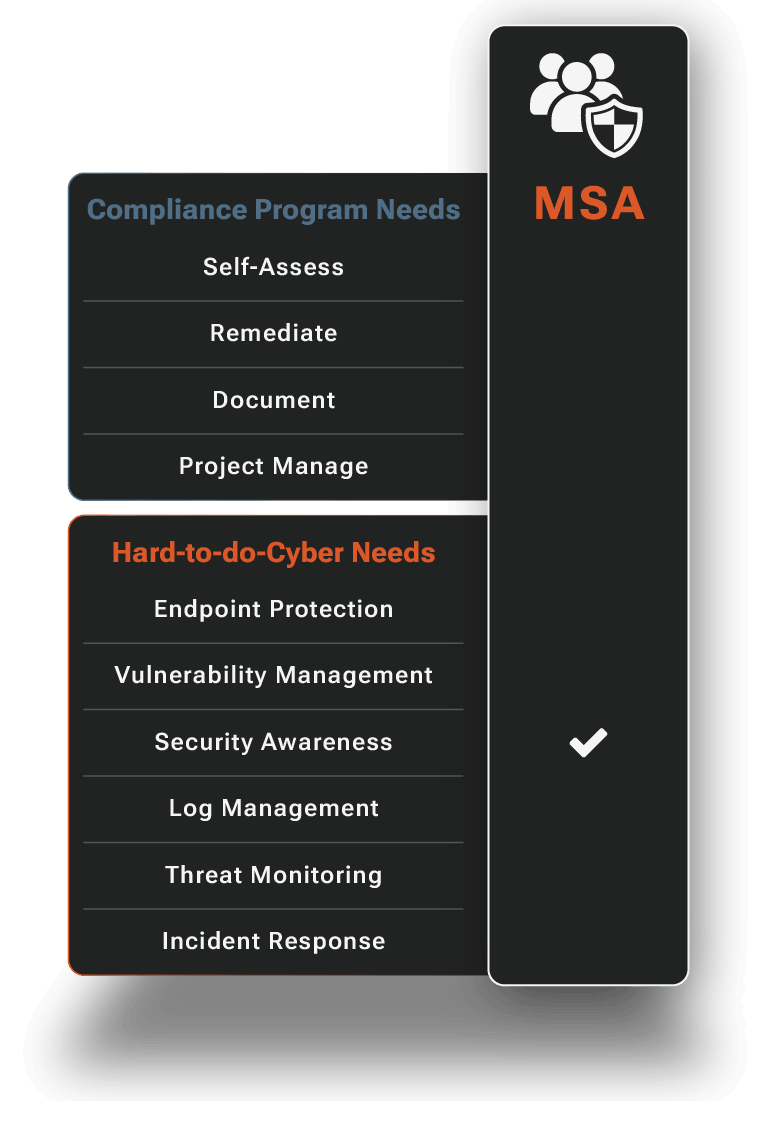
Managed Security Awareness
People are too often the weak link. We'll shore up your human line of defense with security awareness content, exercises and phishing simulations that’s informed by real threats our vSOC sees every day.
- Comprehensive Annual Training
- Ongoing “Bite Sized” Training
- Phishing Attack Simulations
- Ever Evolving Expert Content
- Security Awareness Posture Visibility
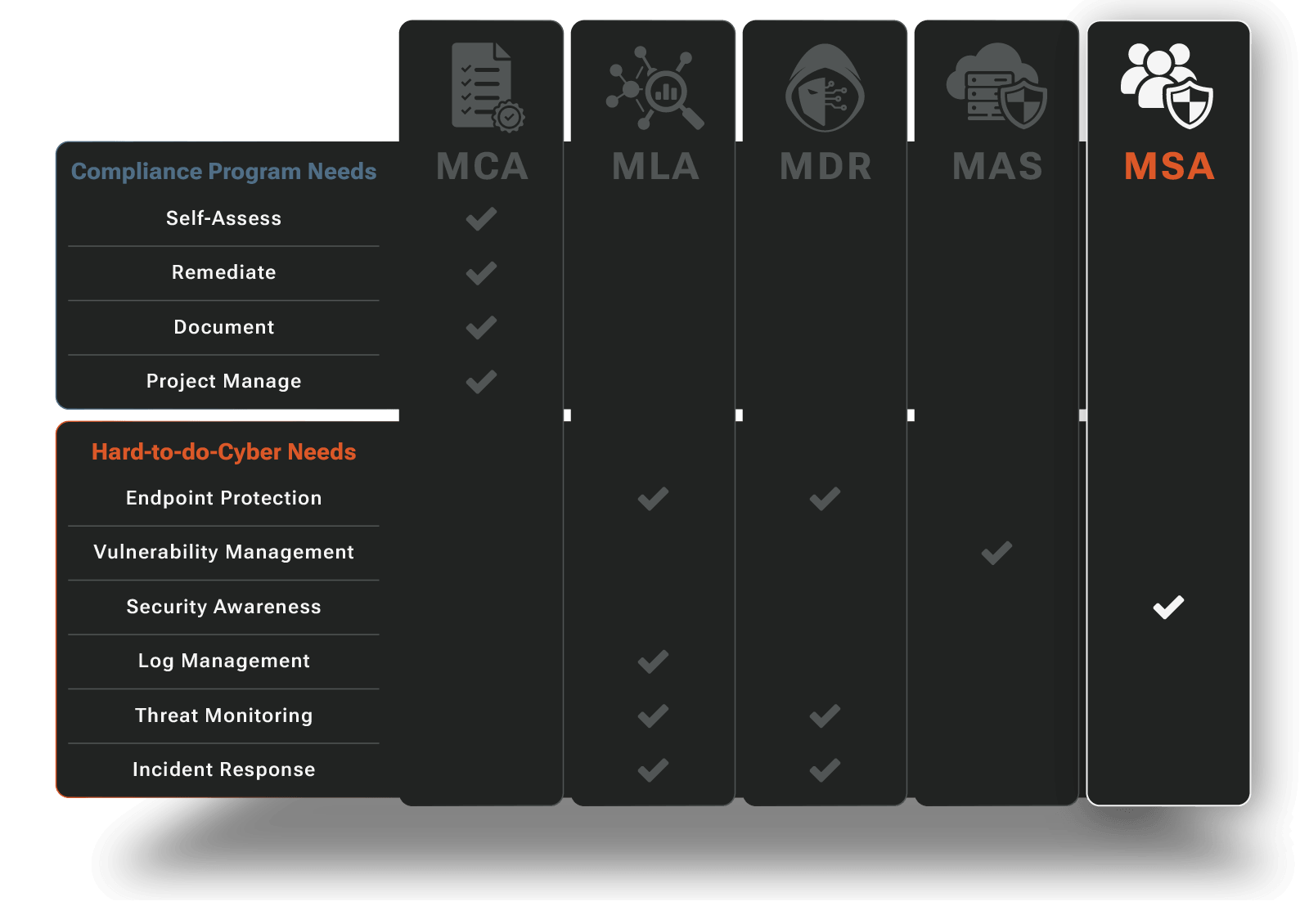
RADICL Pricing
If you’re evaluating a managed SOC service, pricing typically depends on environment size, coverage scope, and required compliance support. We’ll help you scope the right level of coverage without overbuying.
Frequently Asked Questions
Do I need a SOC if I’m an SMB?
You need SOC operations, not necessarily SOC infrastructure and a team.
Modern cyber threats—ransomware, business email compromise, credential theft—require 24/7 monitoring, expert triage, and coordinated incident response. That's what a Security Operations Center does. But building one (hiring analysts, deploying platforms, establishing workflows, maintaining 24/7 coverage) isn't operationally viable for most SMBs.
RADICL is your SOC. We deliver the operations: monitoring, investigation, response coordination, documentation without you having to build the infrastructure or hire the team.
Can you work with my MSP (and will you replace them)?
RADICL complements MSPs, We don't compete with them. Your MSP handles IT execution (servers, networks, helpdesk, infrastructure). RADICL handles security operations (monitoring, triage, incident response, vulnerability prioritization, compliance evidence). In practice:
- Your MSP stays your primary IT partner and keeps the customer relationship
- RADICL monitors for threats, investigates incidents, and coordinates response
- When remediation is needed, we define the work and your MSP executes it (or you do, depending on your setup)
- We establish a clear Shared Responsibility Matrix so everyone knows who owns what
Most MSPs appreciate this because we handle the security operations layer they can't staff, without trying to take over IT delivery.
What happens when there’s an incident? Who does what?
RADICL leads, you approve, your team executes (when needed). Here's the typical flow:
- Detection & Triage (RADICL) Our analysts detect the activity, validate it's a real threat (not noise), and immediately create a Case documenting what we found.
- Investigation (RADICL) We investigate scope and severity—how far did the attacker get, what data was accessed, what systems are affected. If we need context from your environment, we'll send a specific Inquiry.
- Response Coordination (RADICL) We define the containment and remediation actions required and create Workflow Tasks with step-by-step guidance. This might be: isolate this endpoint, reset these credentials, block this IP, etc. We execute actions that you have approved.
- Execution (You or Your MSP) Your team executes any actions that are business sensitive per our responsibility matrix. We don't make changes in your environment without approval—but we tell you exactly what needs to happen.
- Tracking & Closure (RADICL) We track every task to completion and document the outcome. Incidents don't linger, and "done" actually means done.
- Post-Incident Hardening (RADICL) After containment, we recommend configuration changes, additional detections, and hardening measures to prevent recurrence.
You stay in control. We provide the expertise and coordination.
How do you avoid overwhelming us with alerts and vulnerabilities?
Two ways: triage and prioritization.
On Alerts: We don't forward raw security alerts to you. Our analysts triage every detection to determine what's real, what's noise, and what requires action. You only hear from us when there's something meaningfulnand it comes as a documented Case with context, not just an alert.
On Vulnerabilities: Through Managed Attack Surface (MAS), we scan your environment continuously but prioritize remediation based on:
- Exploitability – Is this vulnerability being actively exploited in the wild?
- Exposure – Is the vulnerable system accessible to attackers?
- Business Impact – What happens if this system is compromised?
You get a prioritized remediation queue with step-by-step guidance—not a 10,000-item vulnerability list. We track fixes to closure at a pace your team can sustain, not a panic-driven scramble.
Our job is to filter, prioritize, and coordinate. Not drown you in data.
Can you help with CMMC/NIST 800-171?
Yes. We provide both the technical controls and the compliance operations.
For CMMC and NIST 800-171, compliance isn't just about deploying security tools. It's about continuously validating that controls are working and collecting evidence to prove it. RADICL delivers:
- Technical controls that map directly to CMMC/NIST requirements (endpoint protection, identity monitoring, incident response, vulnerability management)
- Continuous evidence collection so you're not scrambling when assessors show up
- Compliance reporting that shows which controls are validated and which need attention
- Assessment preparation including evidence spot-checks and remediation guidance
We guide the process, validate your controls, and help you prove to assessors that your security program is real—not just checkboxes.
What visibility do we get (dashboards, reporting)?
Real-time visibility into everything we're doing to protect you.
Through RADICL's Protection Delivered Dashboard, you can see:
- Endpoint protection status – Which devices are protected, any coverage gaps
- Threat detections - What we detected, investigated, and how we responded
- Incident management - Active Cases, investigation status, remediation tasks
- Vulnerability posture – Your attack surface, prioritized risks, remediation progress
- Security awareness – Employee training completion, phishing simulation results
- Compliance status – Which controls are validated, which need attention
The dashboard updates in real-time. No waiting for monthly reports to know what's happening. When something is detected, investigated, or resolved, you see it.
Transparency is non-negotiable. You're not buying a black box, you're getting visibility into professional security operations.
How fast can we get up and running?
You're protected in as little as 7 days.
We deploy endpoint protection, establish monitoring, and begin 24/7 operations. You're not waiting months for "implementation"—you're protected immediately.
Over the following weeks, we tune detections to your environment, establish vulnerability prioritization, and optimize workflows.






















