We Worry About Your Cybersecurity
So You Don't Have To
Talk to Our Team!
The SMB Security Gap
Small and mid-sized businesses deserve better:

You're a growing target for cyber attacks

Enterprise solutions aren't built for you

Basic security isn't enough anymore

Most service providers overlook SMBs entirely
Our Solutions
Managed Detection and Response
|
Advanced endpoint protection, military-grade threat hunting, and 24×7 incident response ensure your company is safe from ransomware, data theft, financial fraud, and other high-impact cyber risks while supporting compliance requirements like CMMC and NIST 800‑171.
Endpoints and Servers Protected
Evasive & Embedded Threats Detected and Stopped
24×7 Security Operations Has Your Back
Incidents Managed End-to-End
Virtual CISO By Your Side
|
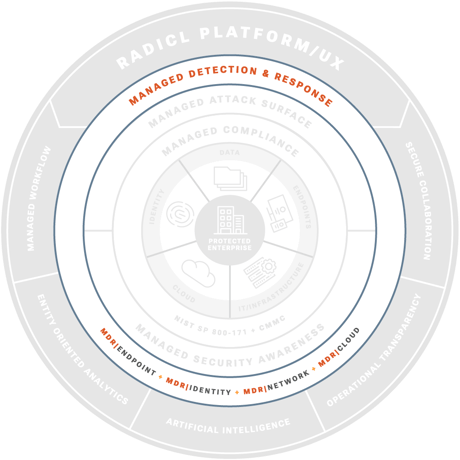 |
MDR | Endpoint
MDR | Identity
MDR | Network
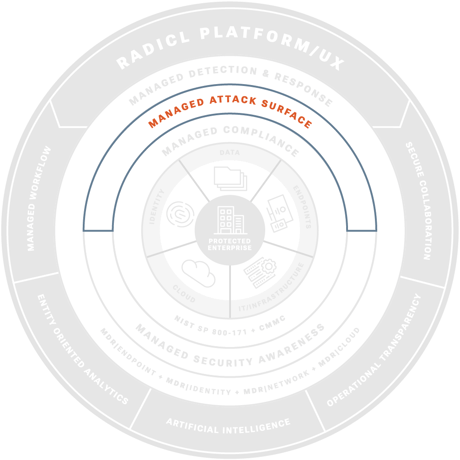
Managed Attack Surface
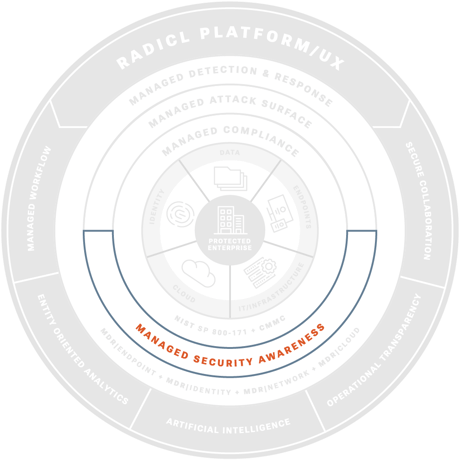
Managed Security Awareness
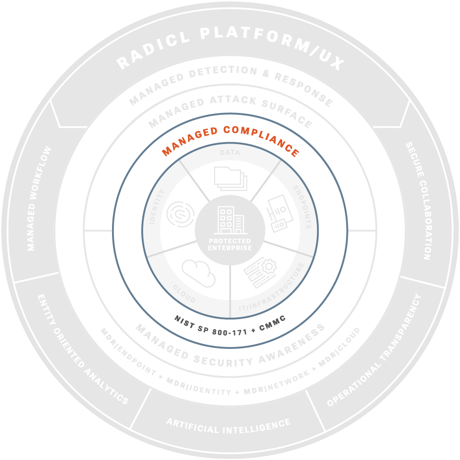
Managed Compliance Adherence
Why Companies Choose

Full Security Operations in 7 Days
Get enterprise-grade protection without building an internal team. We handle everything from monitoring to compliance.
Complete Visibility
Real-time dashboard shows exactly what we're doing to protect your business. No more security black boxes.
True 24/7 Protection
Our virtual Security Operations Center (vSOC) provides round-the-clock monitoring, detection, and rapid response capabilities.
Advanced Threat Hunting
Military-grade threat hunting operations that find sophisticated attacks other tools miss. Built on defense industry expertise.
Cost-Effective Security Operations
Get the security team and technology you need without the overhead of building it yourself. One predictable monthly fee.
What Our Customers Are Saying



How We Compare
When compared to traditional managed service offerings, RADICL goes above and beyond in depth and bread of delivered cybersecurity capabilities and protection.

The RADICL Path to Stronger Security

Initial Consultation
We honestly evaluate your current security needs and whether we can help.
7 Day Deployment
In 7 days, your vSOC is live, endpoints protected, 24/7 threat response ready.

Continuous Ops
Ongoing security posture improvements and compliance adherence.
Ready to Stop Managing Security and Start Running Your Business?
RADICL delivers enterprise-grade cybersecurity through AI-powered automation and human expertise — purpose-built for SMBs facing nation-state threats.