
Managed Compliance and Cybersecurity Services
Trusted Cybersecurity And Regulatory Compliance — Comprehensive, Fast, Affordable
High‑risk and regulated organizations deserve "military-grade" defense‑in‑depth protection and audit‑ready assurance.
Fully Managed Compliance and Cybersecurity-as-a-Service. Delivered as One.
RADICL acts as your dedicated security operations team and compliance partner. Our autonomous virtual security operations center (vSOC) uses AI-driven workflows and human expertise to deliver threat detection and response, attack surface hardening, and compliance adherence as a single, fully-managed cybersecurity‑as‑a‑service offering.


Hardest-to-Meet Compliance Regulations Off Your Plate
RADICL brings the platform and the experts to meet tough requirements fast, without adding headcount.
Log data centralization, analysis, and review
Centralize the right logs fast without a SIEM science project. We keep them searchable for investigations and audit evidence.
24/7 threat detection & monitoring
Always-on monitoring across endpoint, identity, and infrastructure signals. We surface what’s real and what needs action.
24/7 incident response
When something trips, we investigate and contain it quickly. We own the response and when needed, orchestrate and guide actions required by your IT team or MSP.
Endpoint protection
Managed endpoint protection that’s tuned, monitored, and acted on. We ensure EPP/EDR is optimally configured to ensure trusted proactive protection.
Vulnerability management
Continuous scanning with real prioritization so teams fix what matters most first. We track remediation to closure and verify results.
Security awareness training
Training and simulations tied to real attack patterns we see in the wild. Reduce click risk and reinforce the behaviors auditors expect.
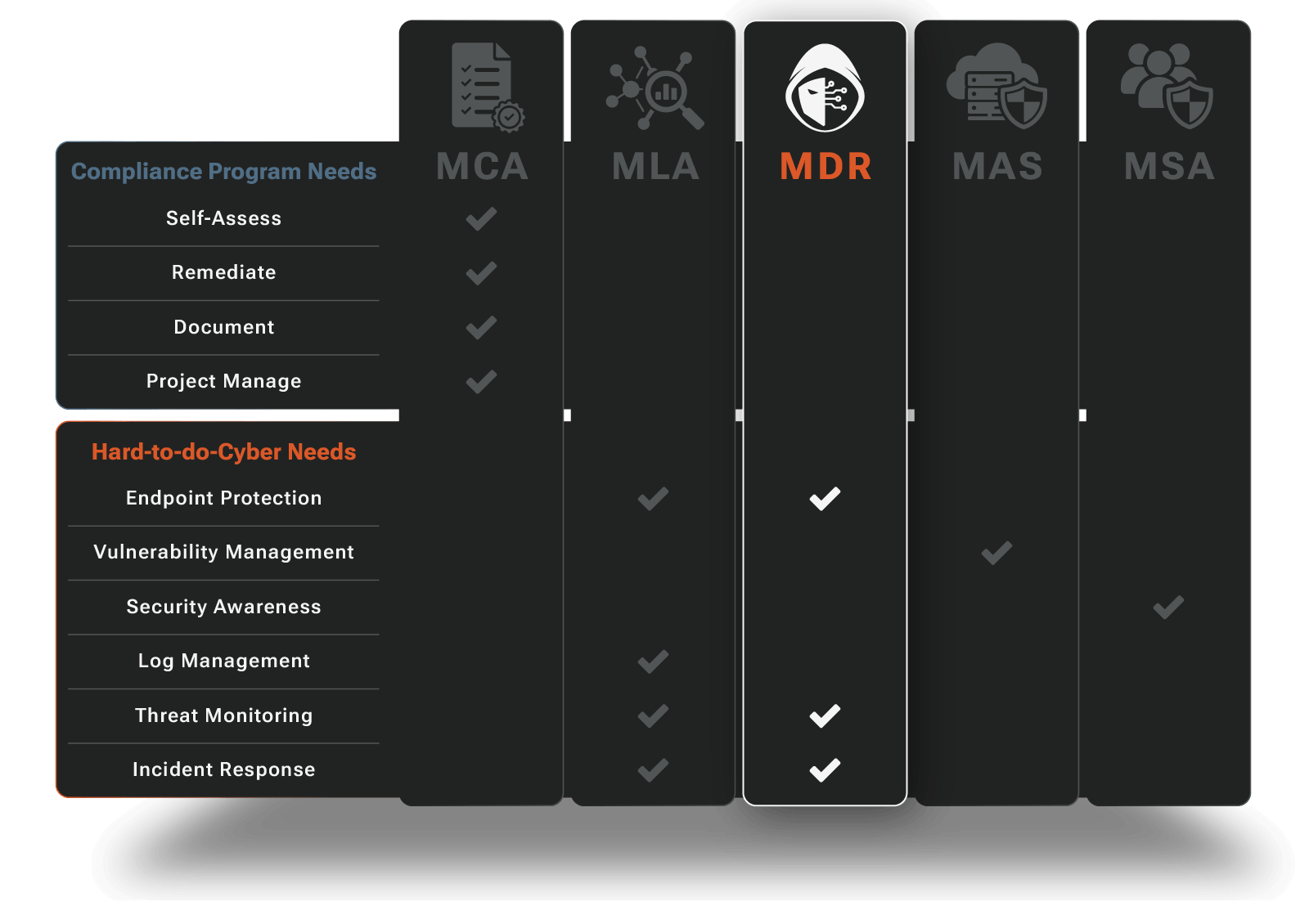
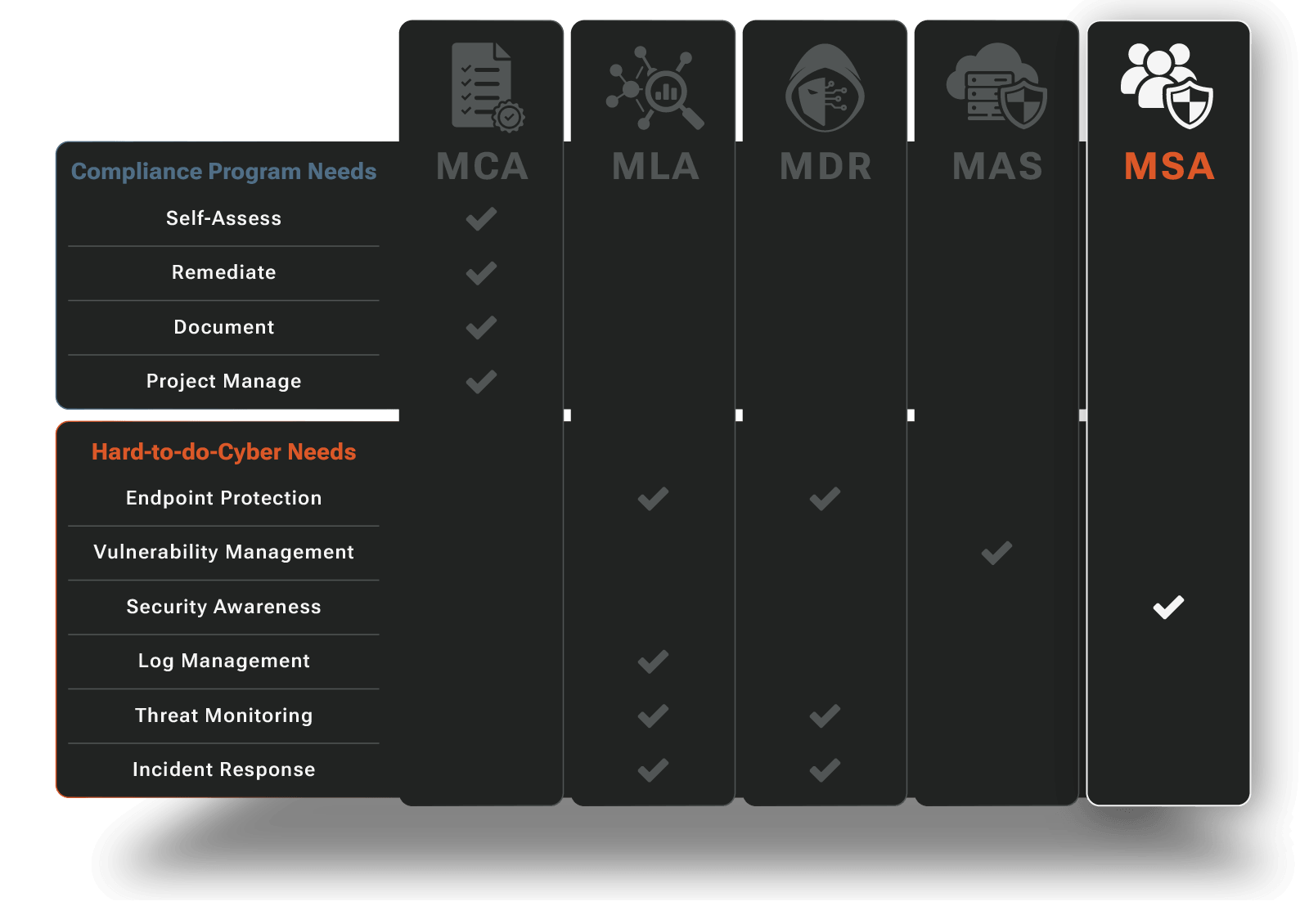
Our Solutions
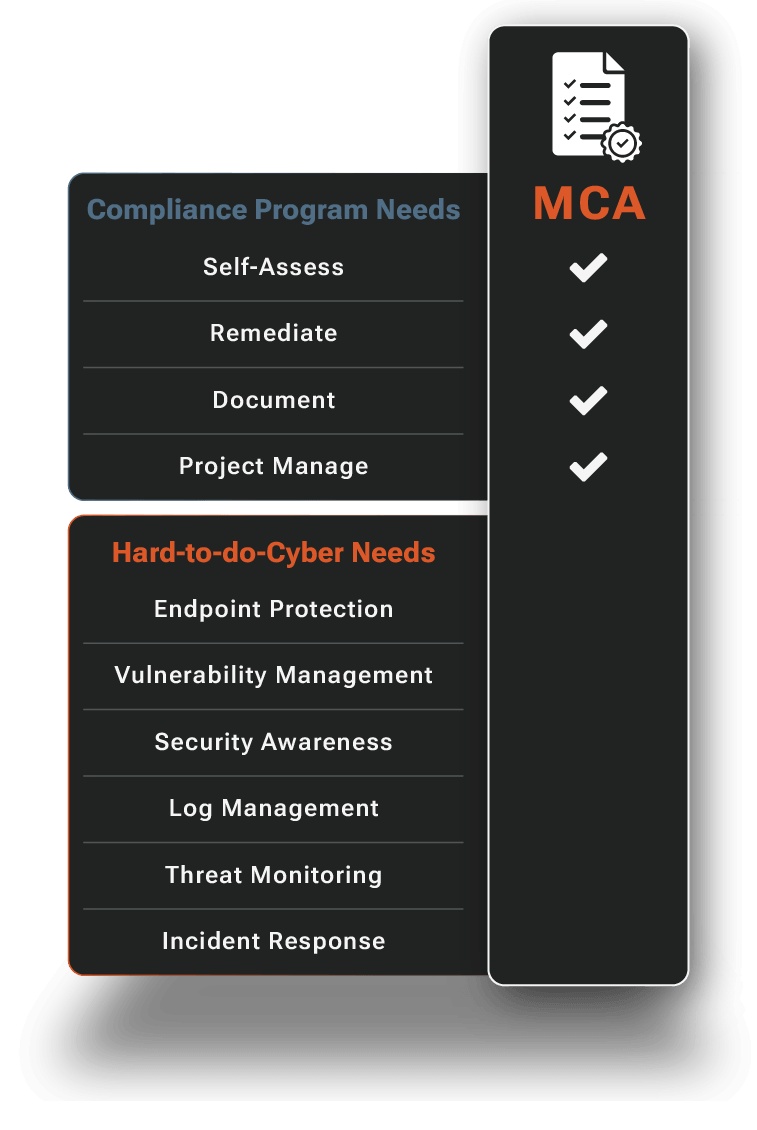
Managed Compliance Adherence for CMMC and NIST
CMMC and NIST 800‑171 (and similar frameworks) are now a cost of doing business. We keep the cost low. Our Managed Compliance Adherence expertly guides and manages your compliance journey. Our compliance experts combined with agentic automation fast track readiness and reduce audit anxiety.
- Self-Assessments Guided and Made Easy
- CMMC and NIST Adherence Gaps Quickly Closed
- Audit Trail and Evidence Capture
- Compliance Posture Clarity
- External Audit Preparedness & Efficiency
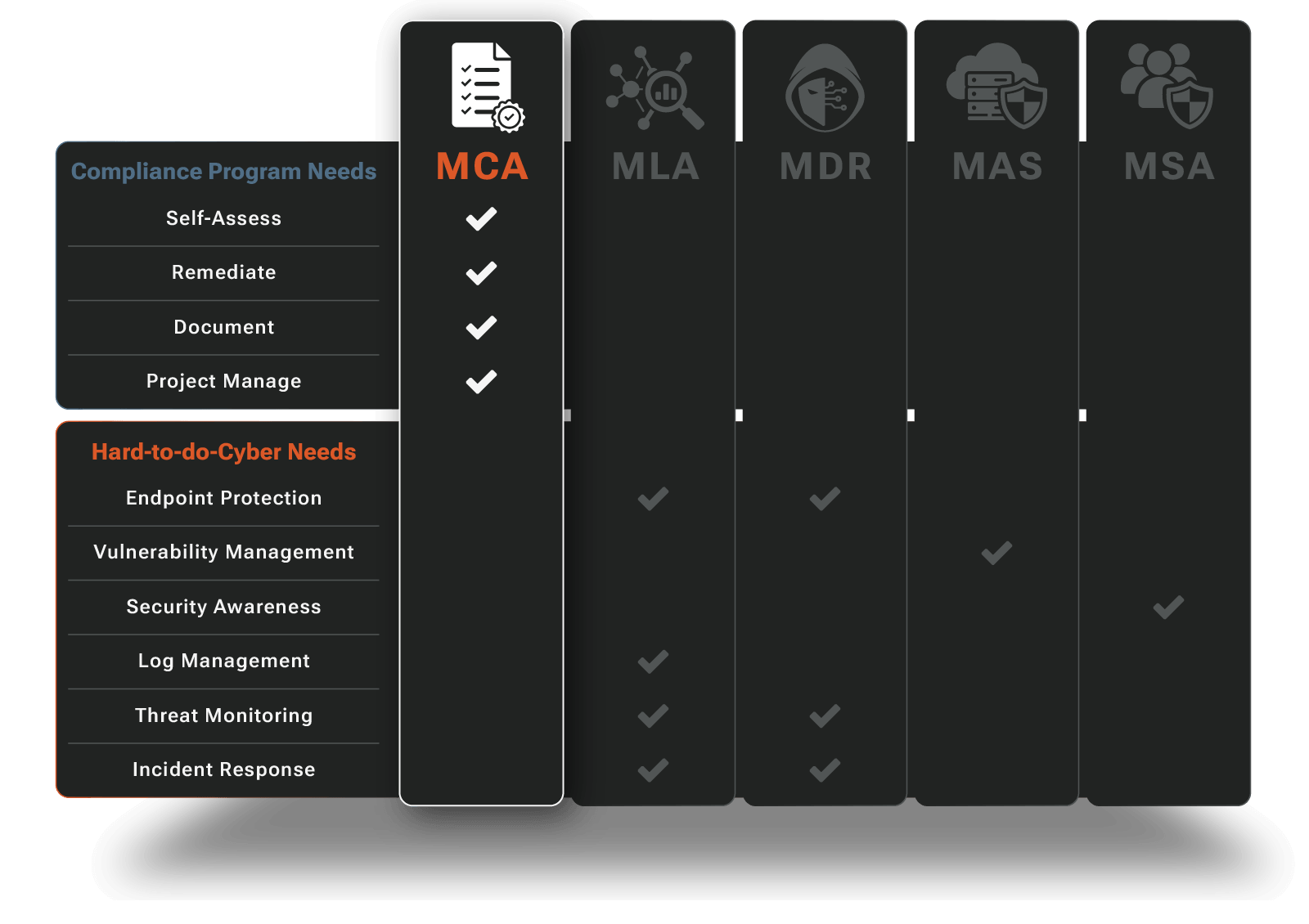
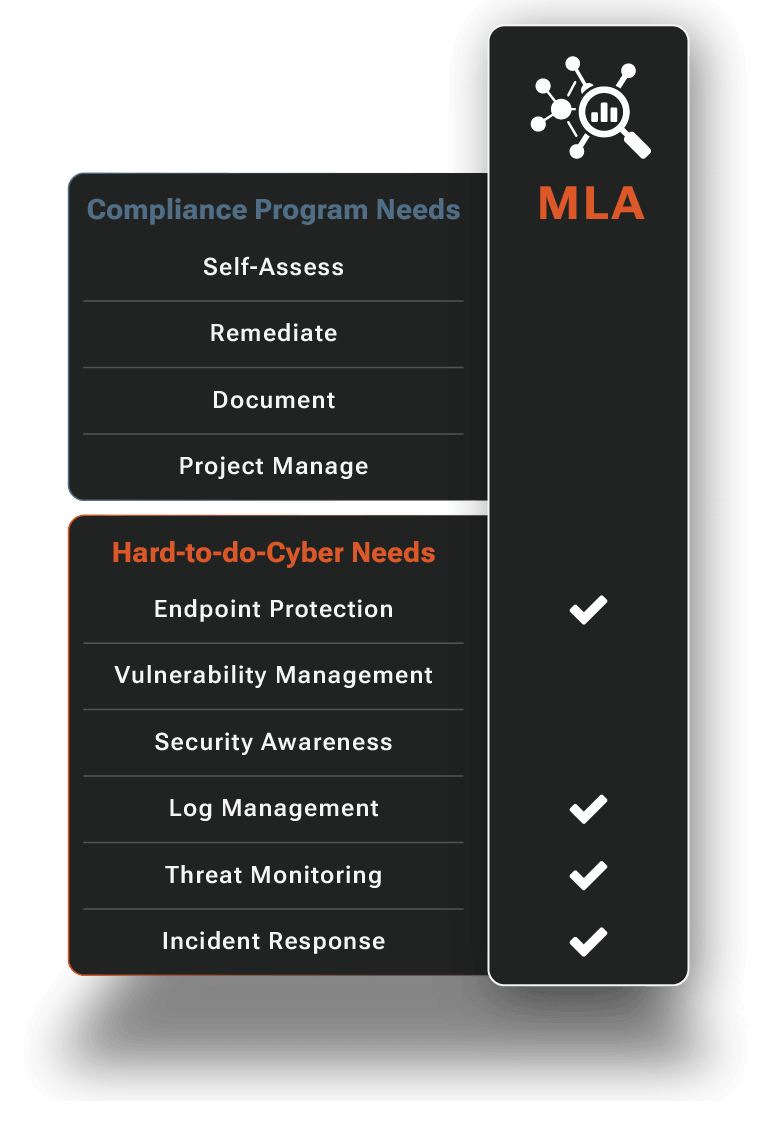
Managed Log Analytics
Investigations and audits require comprehensive visibility, but aggregating logs across your entire environment can be complex and expensive. Not with us.
We handle the entire log management lifecycle, from collection and normalization to long-term retention and searchable investigation capabilities. Our platform gives you the log foundation needed for effective detection & response while meeting strict compliance requirements.
- 14 or 90-Day Velocity Search + 1-Year Archive
- AI-Assisted Natural Language Search
- Hunt UX with vSOC Incident Escalation
- On-Demand Compliance Evidence Export
- vSOC-Managed Ingestion & Health Monitoring
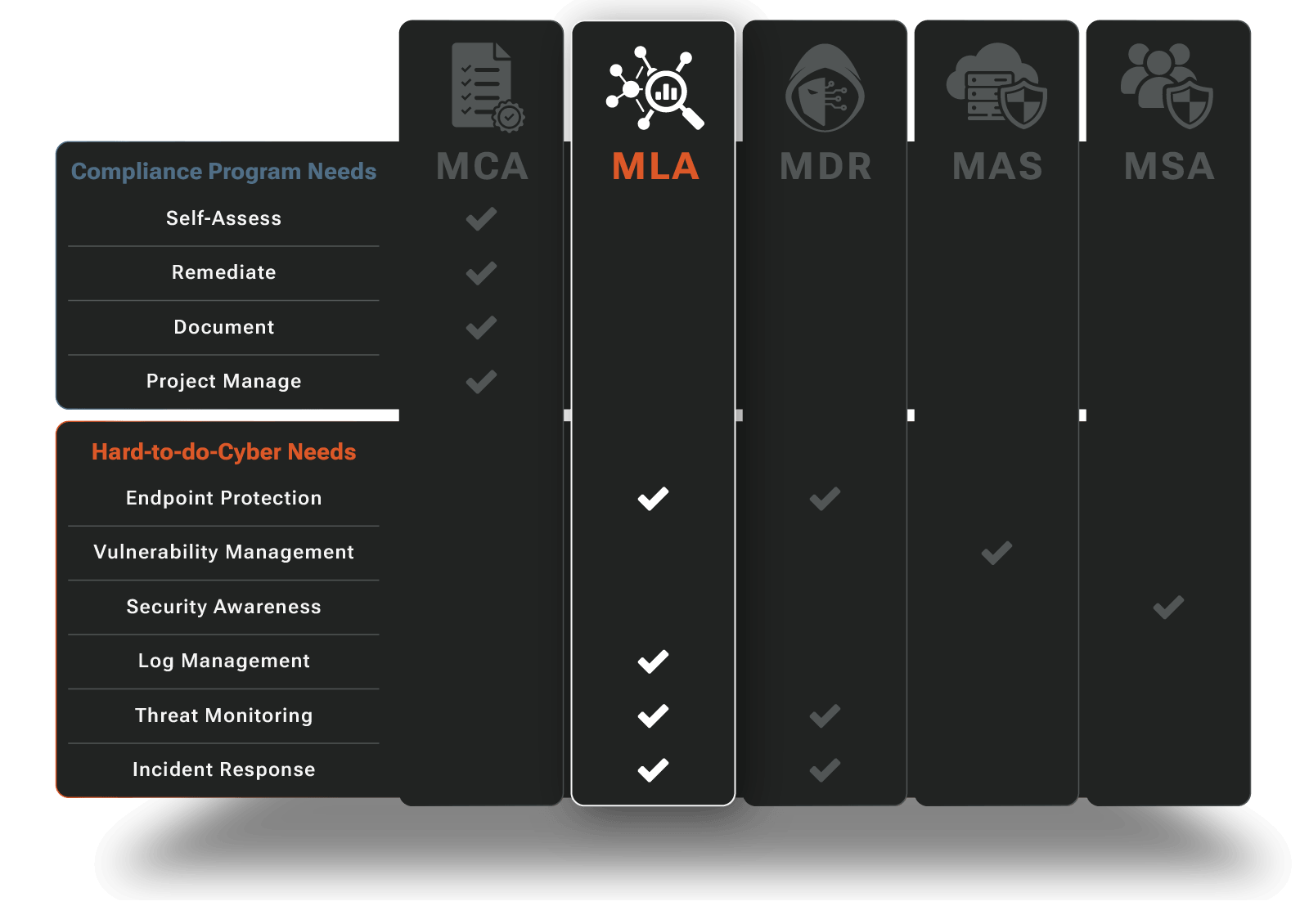
Managed Detection
and Response
Advanced endpoint protection, military-grade threat hunting, and 24/7 incident response ensure your company is safe from ransomware, data theft, financial fraud, and other high-impact cyber risks while supporting CMMC and NIST 800‑171 compliance.
- Endpoints and Servers Protected
- Evasive & Embedded Threats Detected and Stopped
- 24/7 Security Operations Has Your Back
- Incidents Managed End-to-End
- Virtual CISO By Your Side
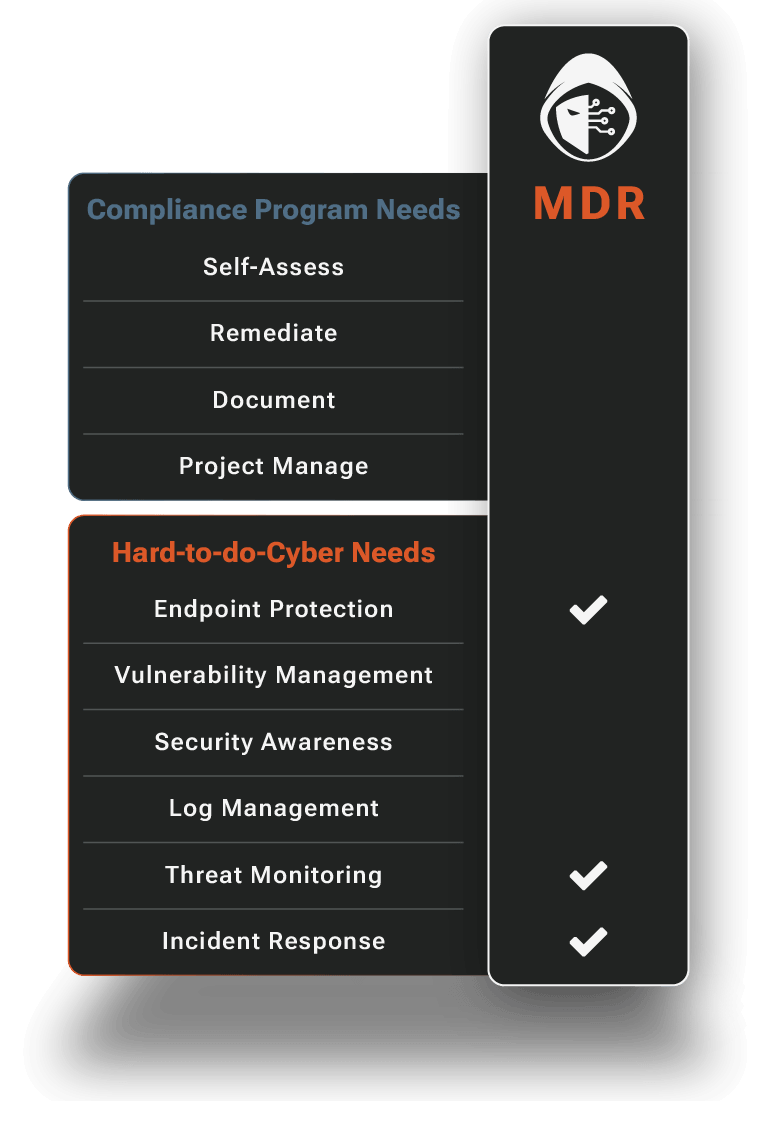
MDR: Endpoint
MDR: Endpoint is the foundation of our MDR offering. We deploy, optimize, and maintain leading EDR technologies (for example, CrowdStrike, SentinelOne, and Microsoft Defender) across your laptops, workstations, and server infrastructure. We deploy custom detection analytics to spot threats out-of-the box EDR miss.
MDR: Identity
With MDR: Identity, we ingest and analyze data from Identity and user activity data sources like Microsoft 365 and Google Workspace. We monitor authentication activity, access to sensitive data and files, and email behavior to detect account takeover, inbox compromise, and data exfiltration.
MDR: Network
MDR: Network collects alarms and threat data from physical, wireless and cloud network infrastructure. We correlate this with endpoint and identity telemetry to fully investigate suspicious behavior and provide defense‑in‑depth coverage.
How RADICL Detects and Responds
Below is a closer look at our Managed Detection and Response (MDR) operations. This is how we turn signals into 24/7 investigations, containment, and tracked remediation.
Managed Attack Surface
Threat actors leverage vulnerabilities to get a foot in the door and expand their presence. Our Managed Attack Surface offering persistently reduces your exposure so your organization becomes a much harder target for both opportunistic and targeted attacks.
- Endpoint and Server Vulnerabilities Detected and Prioritized
- Pragmatic and Manageable Remediation Pace
- Accelerated Critical Fix Response
- Expert Guidance and Collaboration With Your IT/MSP Partners
- Closed Loop “Fixed” Visibility
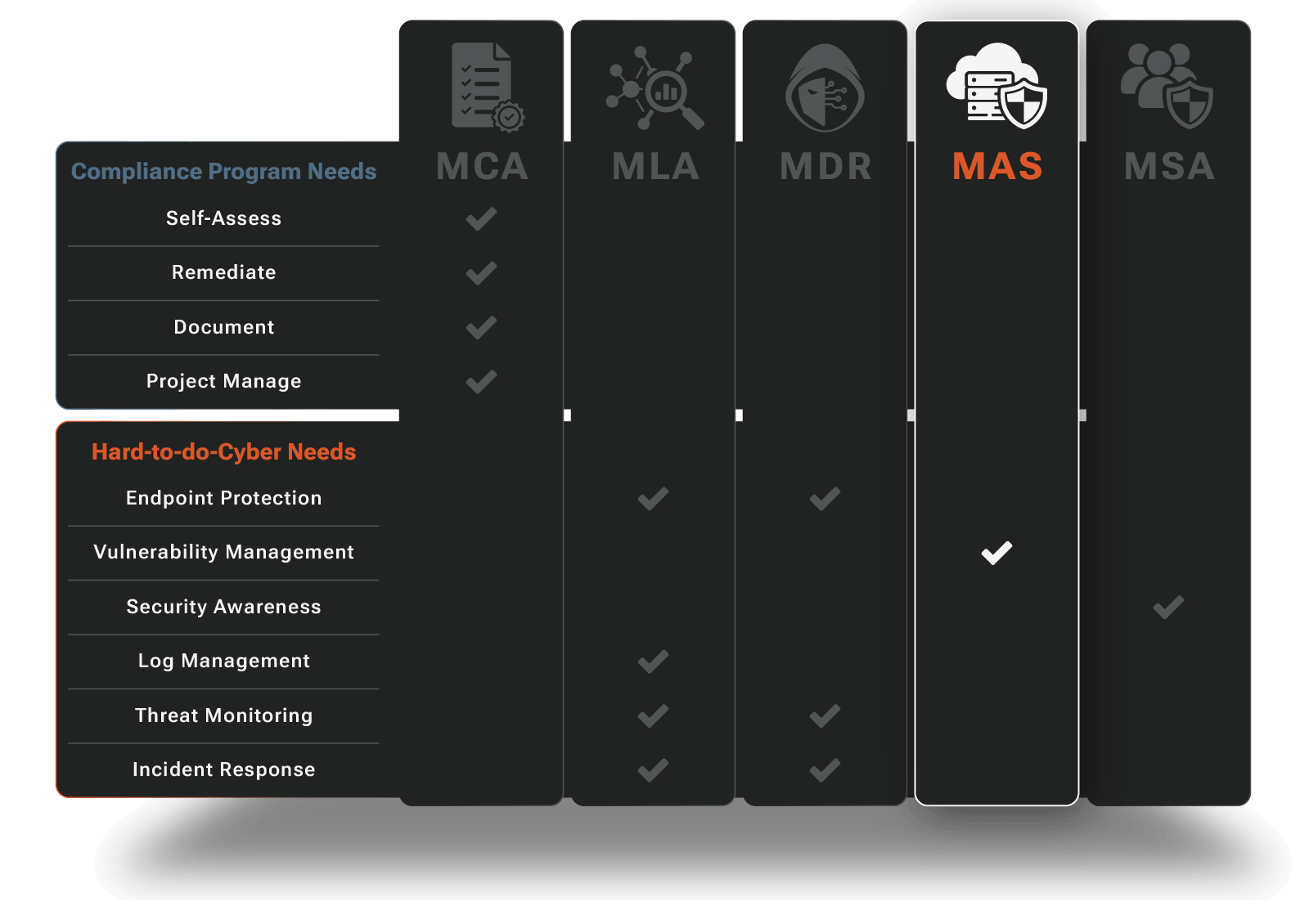
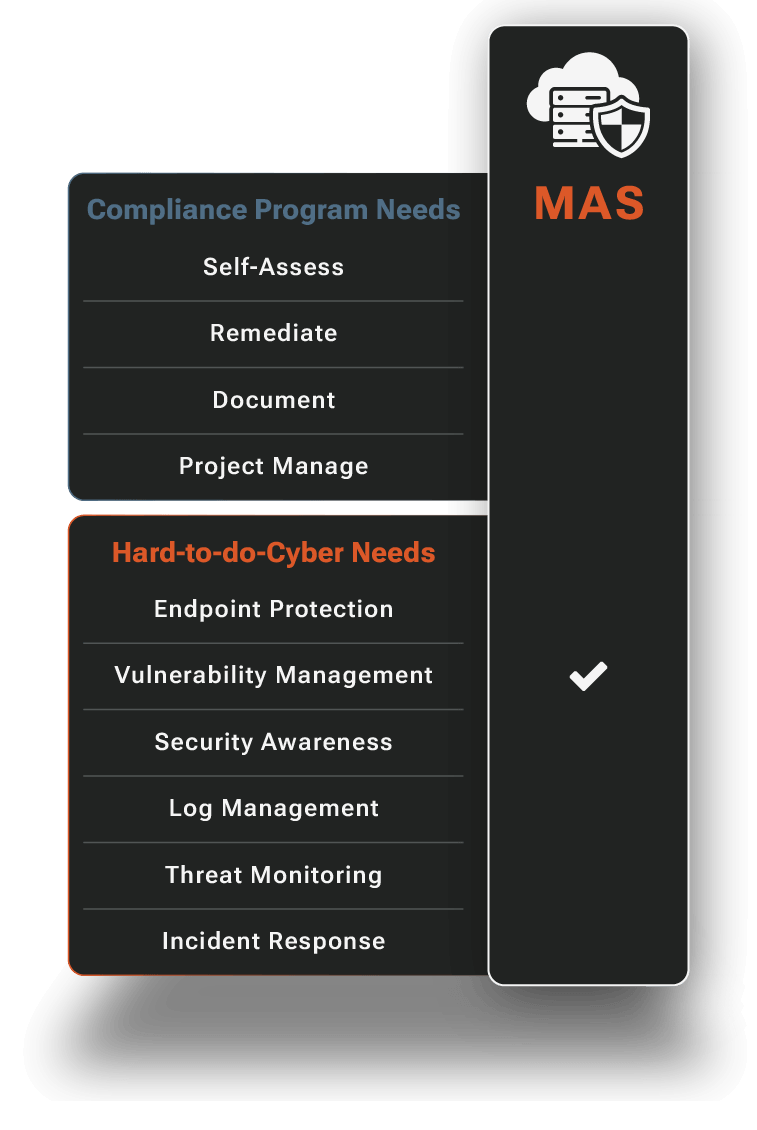
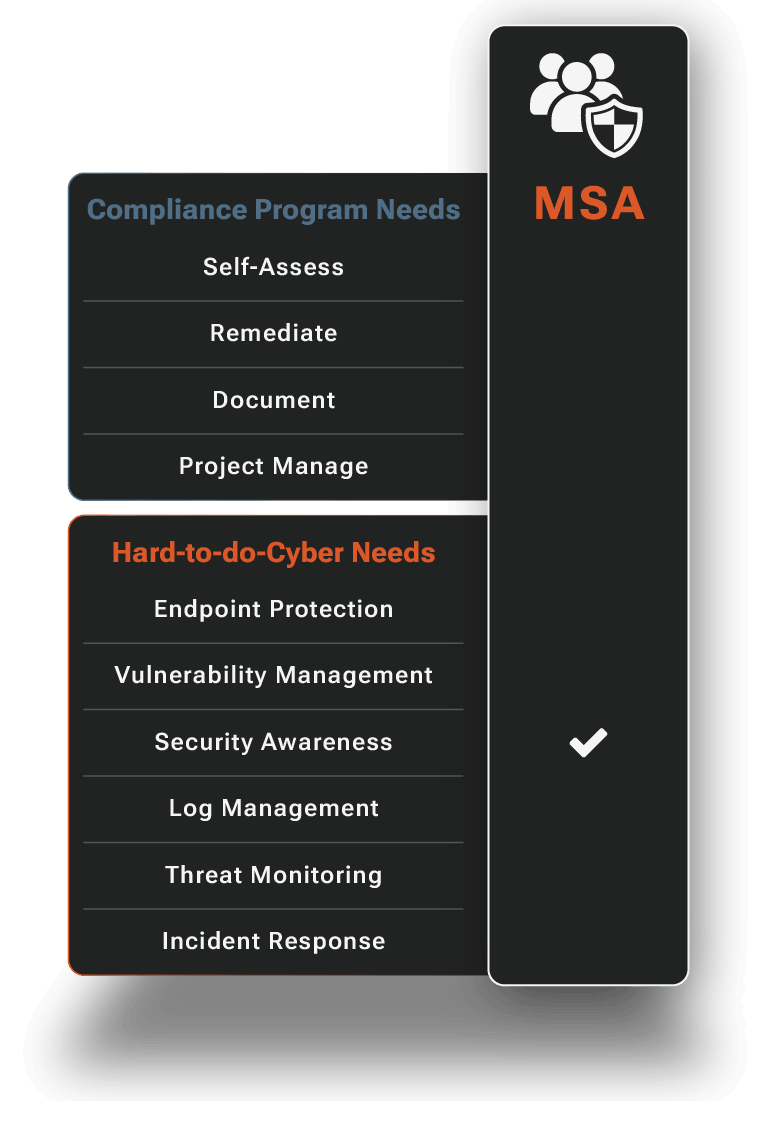
Managed Security Awareness
People are too often the weak link. We'll shore up your human line of defense with security awareness content, exercises and phishing simulations that are informed by real threats our vSOC sees every day.
- Comprehensive Annual Training
- Ongoing “Bite Sized” Training
- Phishing Attack Simulations
- Ever Evolving Expert Content
- Security Awareness Posture Visibility

Made fast. Made affordable. Powered by AI.
Our autonomous vSOC, powered by the proprietary RADICL Platform, becomes your security operations team by combining agentic and AI augmented workflows with expert human oversight to improve speed, accuracy, and affordability, while staying transparent and collaborative with your IT team and MSP. From onboarding to day-to-day activities, RADICL Platform is designed to be transparent, collaborative, and easy for busy leaders and IT teams to work with.
Our Agents are trained and supervised by our vSOC, cybersecurity and compliance experts who apply their experience and knowledge, combined with the strengths of our platform, to keep you secure, compliant, and audit-ready.

What RADICL Protects You From
Cyberthreats come from every direction and are evolving faster than ever with AI. Avoiding and detecting them requires fighting AI with AI via technology that unifies agentic operations and human expertise into a cohesive fighting force.
The RADICL Platform delivers DeepThreat™ protection and visibility into the full range of cyberthreats facing regulated and high‑risk SMBs, so threats can’t disrupt your business, your customers, or your compliance posture.
RADICL helps protect you from all of the following threats, and hardens you to new risks in the future.
Phishing
We limit phishing success through security awareness backed up by inbox monitoring and blocked payloads.
Financial Fraud
We equip employees to deter social engineering and monitor for fraudulent activity.
Email & Account Compromise
We monitor M365 and Google Workspace accounts to quickly respond to takeover signals.
Data Theft & Insider Risk
We collect and analyze user activity to detect and stop abnormal data access and exfiltration.
Advanced Persistent Threats (APTs)
RADICL DeepThreat™ combines continuous analytics with intelligence-driven hunts to detect evasive and embedded threats.
Why Companies Trust RADICL
Predictable Costs: One Platform, One Experience, One Bill
Get the vSOC team, platform, and CMMC‑aligned operations for a predictable monthly fee, made more affordable through automation.
Advanced Threat Hunting
Detect silent, evasive activity missed by other tools (and typical MDRs). Stay ahead of sophisticated adversaries targeting sensitive data.
Accountability via Transparency
No black-box services. With direct platform access, you can see what we see and verify what has been done on your behalf. Trust earned via transparent operations.
Agentic + Expert Operations
Get speed with accountability when AI handles high-volume triage and our human experts handle judgment and response.
Grow as You Go
Start with compliance readiness and/or core protection, then expand as requirements and risk increase.
What Our Customers Are Saying



Frequently Asked Questions
What makes RADICL different from an MSP or typical MDR provider?
Most MSPs focus on keeping your systems running, and most MDR providers drop a sensor on your endpoints and call it done. RADICL CSaaS hardens your entire organization including people, processes, and technology while actively hunting threats around the clock across your whole attack surface. And everything we do is tied directly to your CMMC and NIST 800-171 compliance obligations, which is something MSPs and commodity MDR vendors simply aren't built to deliver.
Can RADICL help us get ready for CMMC and NIST 800-171?
Yes, and this is core to what we do, not an add-on. RADICL CSaaS was purpose-built for the Defense Industrial Base, and we understand the 110 practices of NIST 800-171, the CMMC assessment process, and what assessors actually look for. We close your security gaps, build the documentation and evidence you need, and continuously maintain the compliance posture required for certification.
How quickly can RADICL get us protected and on a CMMC compliance path?
Most customers are actively protected within the first few weeks of onboarding since we deploy detection and response capabilities fast so you're not exposed while compliance work gets underway. Our platform automatically calculates your compliance score and organizes evidence soon after deployment, so you have a clear picture of where you stand without waiting on manual assessments. Our fastest customers reach CMMC readiness in 17 weeks, and we build a prioritized remediation roadmap to get you there as efficiently as possible.
Will RADICL replace our MSP or internal IT team?
No, your MSP or IT team handles infrastructure, helpdesk, and day-to-day operations, and we're not trying to change that. RADICL CSaaS augments your existing team, filling the specialized security gap that most IT providers aren't staffed or equipped to cover while also making sure remediation work is actually getting completed and not falling through the cracks. Think of us as the security layer your IT team has always needed but couldn't build themselves.
What does RADICL actually take off my plate day-to-day?
You're no longer responsible for watching security alerts, triaging threats, chasing vulnerabilities, or figuring out whether something is a real incident or noise since RADICL CSaaS handles all of that continuously. We track your compliance posture so you're never scrambling before an assessment, and we surface what needs to be fixed across your attack surface. You stay informed through clear reporting without having to become a security expert to understand it.
Does RADICL integrate with our existing MDR, EDR, and security tools?
Yes, RADICL CSaaS is built to work within the Microsoft security ecosystem and integrates with leading platforms including SentinelOne, CrowdStrike, and others that DIB contractors already have or are moving toward. If you have existing EDR, email security, or identity protection in place, we layer on top, fill the gaps, and centralize visibility. We're not here to rip and replace, we're here to make your existing investments actually work together and ensure nothing falls through the cracks.
How does RADICL verify remediation work and prove compliance to auditors?
We don't just tell you something is fixed, we verify it and maintain the evidence trail auditors require. Our platform automatically ties security activity to specific NIST 800-171 and CMMC practices, calculates your compliance score in real time, and organizes evidence so when an assessor asks for proof, you have it ready. We help you build and maintain your System Security Plan and supporting artifacts so your documentation reflects your real security posture, not a best-case snapshot.
What happens during a security incident when RADICL is my vSOC?
When our analysts detect a threat, we investigate, contain, and coordinate response in real time, and you're notified with clear, actionable information about what's happening and what we're doing about it. Depending on your service level, we can take direct containment actions including isolating affected systems, blocking malicious activity, and removing threats. After the incident, we conduct a full debrief and help close the gaps that made the attack possible in the first place.
Is RADICL built only for DIB contractors, or can other high-risk SMBs use it too?
RADICL CSaaS was designed for the DIB since the compliance requirements, threat landscape, and operational realities of defense contractors are baked into everything we do. That said, the model translates well to any high risk SMB operating in regulated industries or handling sensitive data where a commodity security solution isn't enough. If your organization needs real security outcomes and not just checkbox compliance, RADICL is built for that.
How is RADICL CSaaS different from a legacy MSSP or MDR provider?
Legacy MSSPs sell you a monitoring service and flood you with alerts, while traditional MDR providers focus narrowly on endpoint detection and leave the rest of your environment exposed. RADICL CSaaS is comprehensive by design, combining detection and response, attack surface management, automated compliance scoring, evidence organization, and security awareness into a single integrated service tied directly to NIST 800-171 and CMMC practices. You get a security partner accountable for your actual security posture, not a vendor selling you tools and walking away.
What do you mean by "autonomous SOC"?
A traditional SOC relies on analysts manually reviewing alerts, investigating threats, and escalating issues, which is slow, expensive, and impossible to staff effectively at the SMB level. RADICL CSaaS uses AI-driven detection and automated response workflows to handle high-volume, repetitive work at machine speed so our human analysts can focus their time on real threats that require judgment. The result is enterprise-grade security operations delivered at a price point and scale that actually works for defense contractors.



























